Trust Me Bro
Dw about me boss, this process is just one of the bois
EDR? I hardly know 'er 😏
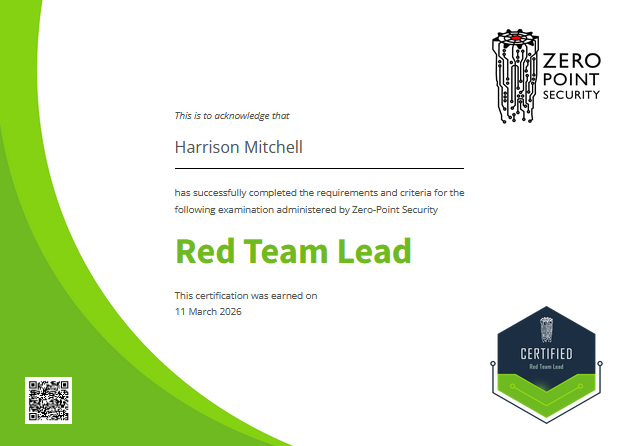
I had Zero-Point Security's Certified Red Team Lead course shouted for me, so it'd've been a shame not to smash it out.
So over a sick week I poured over the course, punched through the labs and YOLO'd the exam to gain those gorgeous CRTL letters for my profile / resume.
Many of my thoughts from Zero-Point's prereq CRTO course carry over, so assuming you've read them I'll spare you from my already sung praises for the overall quality of Rasta's courses.
The course was well laid out and nicely flowed as you carried it out; introducing concepts one at a time. Starting out was a bit rough because the learning curve was a wall - but going from the theory to the labs made it click as to how all the daunting pages of low level code looked in practice and how realistically 99% of it is already done for you by various infosec researchers.
Exam
You're operating in a fully patched Windows 11 / Server 2025 environment with Elastic EDR - which has most of the bells and whistles of more notable EDRs but is FOSS which is nice for spinning up your own instances in a lab to muck around with.
I had fears the exam would contain AD-oddities that would send me on wild rabbit holes but the lab is similar to CRTO in that it's stripped down to only precisely what you need. There aren't 100s of user and group relationships or noisy file systems, Rasta just wants to see if you can apply all the OpSec considerations in the course to a very basic, fully patched AD environment.
The foothold / privesc was my biggest rabbit hole which I'm ashamed to admit because it was staring at me - but in my defense it was quite atypical and relies on you studying what tools you have available (which I failed to do properly).
Nuking IOCs, spoofing call stacks, and untangling syshooks to step around all of EDRs rulesets was a blast - the cat and mouse game that is infosec marches on...